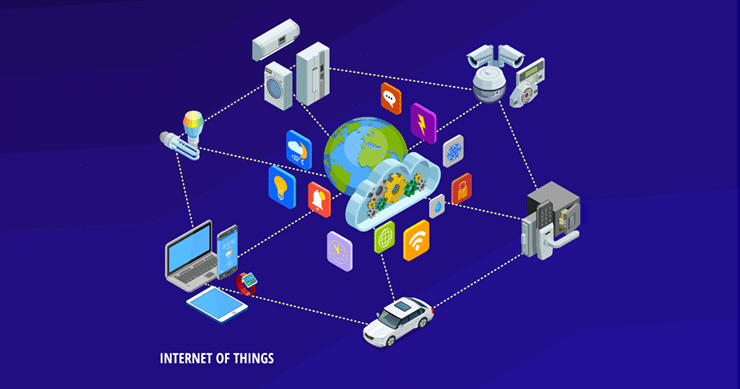
The term IoT (Internet of Things) refers to physical devices, vehicles, appliances, and other objects embedded with sensors, software, and internet connectivity, enabling them to collect and exchange data through the web. In the context of cybersecurity, IoT poses unique challenges and considerations due to its vast scale, unstandardized technologies, and potential vulnerabilities. IoT can have many different associations in the realm of cybersecurity.
For example:
- IoT Devices: Physical objects or devices (e.g., smart thermostats, wearable fitness trackers, industrial sensors) that connect to the internet and interact with other devices or systems.
- IoT Security: The measures and practices implemented to protect IoT devices, networks, and data from unauthorized access, cyber threats, and potential risks.
- IoT Vulnerabilities: Weaknesses or flaws in IoT devices or networks that can be exploited by attackers, potentially leading to unauthorized access, data breaches, or disruption of services.
- IoT Endpoint: An individual IoT device within a network, such as a smart home camera or a connected medical device.
- IoT Firmware: The embedded software within IoT devices that controls their functionalities, features, and interactions with other devices, often requiring regular updates to address security vulnerabilities.
Understanding these IoT-related terms in the context of cybersecurity may help you navigate the complexities and security considerations associated with deploying and managing IoT devices and networks.
IoT Devices are Rife with Vulnerabilities
Security vulnerabilities plague IoT devices. As we continue to add more devices to our networks, we create more potential entries and exits attackers can use to get in and out. A Mckinsey Global Institute report predicts that by 2025, there are expected to be more than 30 billion IoT connections!
At this rate, IoT devices will continue to significantly expand network attack surfaces, especially when you consider that, in contrast to computers and mobile devices, most IoT devices have less processing power and storage space. Because of this, using firewalls, anti-virus software, and other security tools that could help safeguard them is challenging. In addition, IoT devices are a prime target for skilled threat actors because they leverage edge computing to intelligently aggregate data.
Start Getting Value With
Centraleyes for Free
See for yourself how the Centraleyes platform exceeds anything an old GRC
system does and eliminates the need for manual processes and spreadsheets
to give you immediate value and run a full risk assessment in less than 30 days
How Has the Advent of IoT Impacted the Field of Cybersecurity?
The advent of IoT (Internet of Things) has had a significant impact on the field of cybersecurity, introducing new challenges and considerations. Here are some key ways in which IoT has influenced cybersecurity:
Expanded Attack Surface
With the proliferation of IoT devices, the attack surface has significantly expanded. More devices are connected to the internet, creating numerous potential entry points for attackers to exploit. This increased attack surface requires enhanced security measures to protect against potential vulnerabilities.
Inadequate Security
Many IoT devices have been designed with a focus on functionality and connectivity rather than robust security. This has led to the proliferation of poorly secured devices with default or weak credentials, unpatched vulnerabilities, and insufficient encryption mechanisms. These security weaknesses make IoT devices attractive targets for attackers.
Data Privacy Concerns
IoT devices collect and transmit vast amounts of data, often including personal and sensitive information. Ensuring the privacy and protection of this data has become a critical concern. Organizations must implement strong data protection measures, encryption protocols, and comply with privacy regulations to safeguard IoT-generated data.
IoT Botnets and Malware
IoT devices have been increasingly targeted by botnets and malware. Compromised devices can be recruited into botnets, used for distributed denial-of-service (DDoS) attacks, or leveraged as entry points to infiltrate larger networks. Protecting against IoT-based botnets requires strong device security, network monitoring, and threat intelligence.
Lack of Standardization
The lack of standardized security protocols and practices across different IoT devices and platforms poses a challenge. Varying security implementations and compatibility issues make it harder to establish consistent security controls and mitigate risks effectively.
In light of the lack of a standardized security protocol for IoT devices, the Biden administration said it will launch a cybersecurity labeling program for consumer Internet of Things devices starting in 2023. This labeling system for IoT devices set to be rolled out this year will assist consumers by providing information about the potential risks associated with the equipment they are thinking of installing in their homes or offices. In the UK as well, The Product Security and Telecommunications Infrastructure (PTSI) bill is also expected to be released this calendar year.
Start Getting Value With
Centraleyes for Free
See for yourself how the Centraleyes platform exceeds anything an old GRC
system does and eliminates the need for manual processes and spreadsheets
to give you immediate value and run a full risk assessment in less than 30 days





