Deborah Erlanger
Debra Erlanger is a Cybersecurity Analyst specializing in Governance, Risk, and Compliance (GRC). With a keen focus on cyber risk and compliance, Debra is committed to staying at the forefront of industry developments and continuously expanding her knowledge. She thrives in dynamic environments where she can leverage her strong people, organizational, and IT skills. Debra is known for her effective communication abilities and her dedication to delivering high-quality results.

Deborah Erlanger
Debra Erlanger is a Cybersecurity Analyst specializing in Governance, Risk, and Compliance (GRC). With a keen focus on cyber risk and compliance, Debra is committed to staying at the forefront of industry developments and continuously expanding her knowledge. She thrives in dynamic environments where she can leverage her strong people, organizational, and IT skills. Debra is known for her effective communication abilities and her dedication to delivering high-quality results.
Cisco Raises Concerns Over Surge in Brute-Force Attacks Targeting VPN and Web Services
Cisco has sounded the alarm on a widespread increase in brute-force attacks targeting various devices, including Virtual…
NIST AI RMF
What is NIST AI RMF? As artificial intelligence gains traction and becomes increasingly more popular, it is…
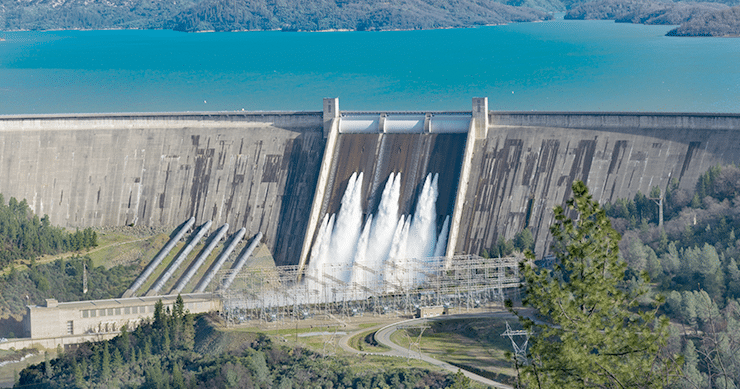
Navigating the Cyber Currents: Ensuring a Watertight Critical Infrastructure
Addressing recent cyber threats, a top White House national security official emphasized the imperative for increased cybersecurity…
Critical Atlassian Flaw Has a Simple Fix
Atlassian has issued a warning about CVE-2023-22518. The severe flaw is described as an “improper authorization vulnerability…
D.C. Voter Data Leak: What We Know So Far
The District of Columbia Board of Elections (DCBOE) has reported a security incident involving the breach of…