Centraleyes Resource Center
- Yair Solow Featured on Bugy's Founder Interviews
- Centraleyes Chosen as Global Top 5 Startups of the Year - Interview
- Centraleyes on Cyber Ghost: Interview with Yair Solow
- Spotlight Q&A with Centraleyes at Safety Detectives
- Centraleyes Expands Automated Risk Register To Cover All Enterprise Risk
- New Centraleyes 4th Generation Release Officially Goes Live
- Yair Solow Featured on VPN Mentor
- Yair Solow on CNN
- CyGov Signs a Strategic Agreement with R3 (Spanish)
- Centraleyes Welcomes Co-Founder of Optiv, Dan Burns, to Its Board of Directors
- Centraleyes Continues to Expand Its Global Network of Strategic Partners with UK-based ITC Secure
- Centraleyes Introduces First Automated Risk Register
- Yair Solow Featured on Website Planet
- Trevor Failor named head of sales at CyGov
- CyGov is rebranding its platform as Centraleyes
- Cybersecurity Company Cygov Partners With Risk Management Company Foresight
- CyGov agrees strategic partnership with top 200 MSSP Cybriant
- Cyber Resilience Resource for Businesses Re-Deploying Remotely
- The Four New Pillars of Corporate Protection Yair Solow on InfoSecurity Magazine
- CyGov selected by SixThirty as Top Cyber Security Startup
- Europe's Top Cyber Security Startups
- CyGov Interviewed by MediaSet
- Eli Ben Meir's article in Security Intelligence
- Yair Solow on i24 News
- CyGov Selected by WorldBank
- Eli Ben Meir OpEd in the Houston Chronicle
- Yair Solow and Eli Ben Meir Present at the SparkLabs Demoday 8
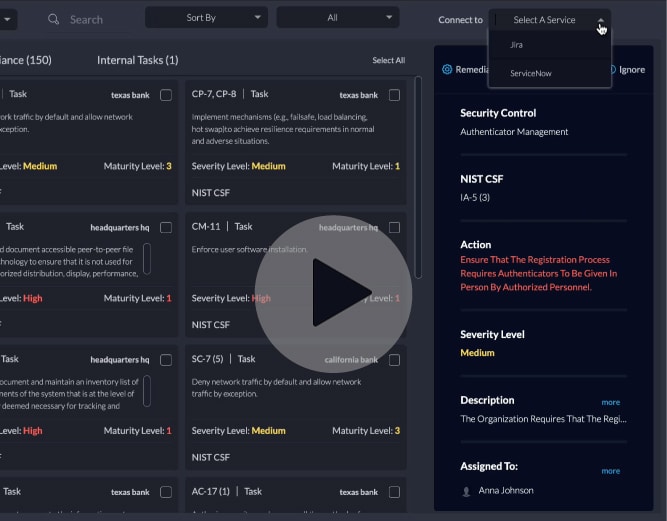
- Enhance Your Cyber Maturity With ITSM Integration and Automated Remediation
- Ensure Your Ongoing Compliance With Automatic Framework Reassessment Tasks
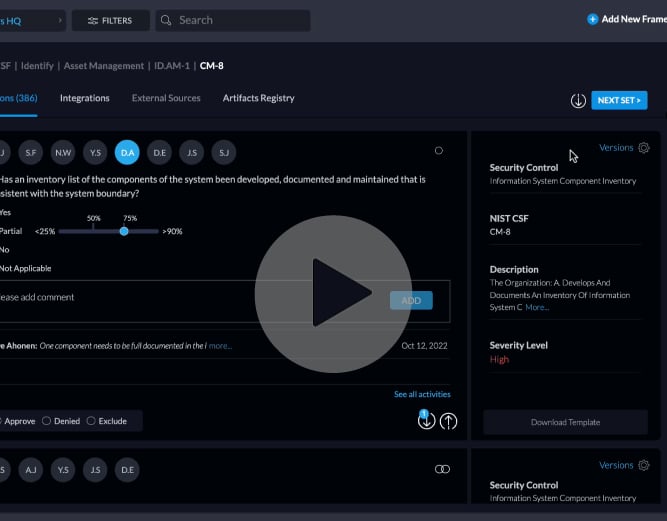
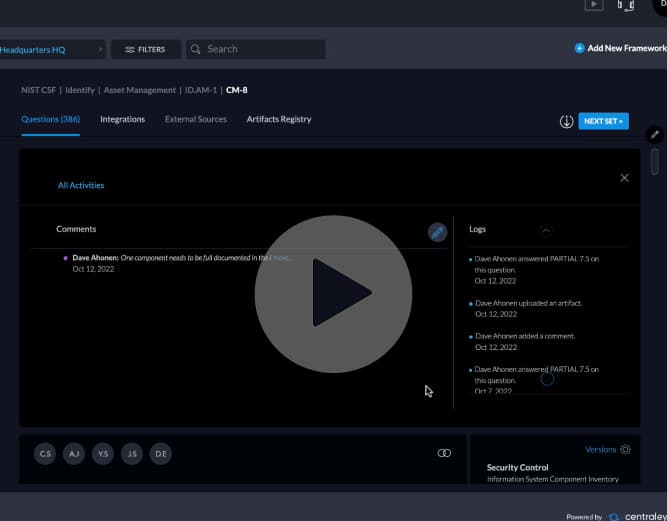
- Stay in the Know With a Full Activity Log of Your Assessment Collection
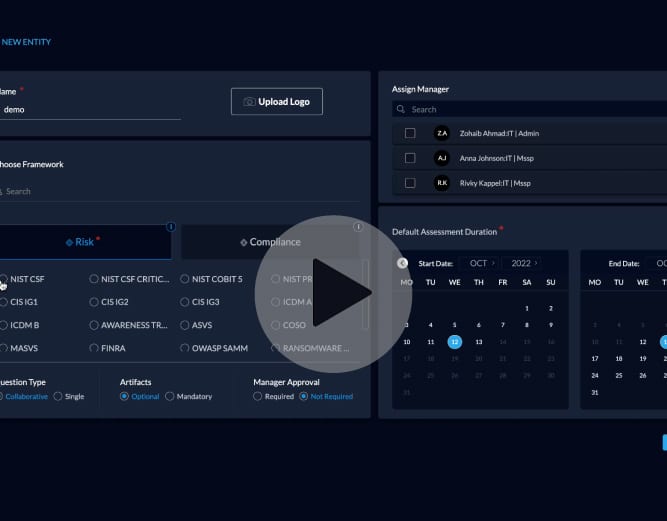
- Add a New Entity to Perform Your Assessment in 10 Seconds
- Quantify Financial Risk With Centraleyes Platform Primary Loss Calculator
- Cover Your Entire Environment With Centraleyes's Risk Application Assessments
- Communicate Cyber Risk With Your Executives in an Intuitive, Beautifully Visualized Board Reporting
- Stay on Top of Your Vendors' Cyber History With In-Depth External Scans
- Automate the Creation and Maintenance of a Risk Register, Saving Hours on Manual Work
- Add a New Framework and Distribute Assessments in Your Organization
- View Your Organization's Risk Scoring Through the NIST Tiering Lens
- Most Intuitive Way for Compliance With the Framework Navigation Tool
- Always Prepared for the Next Task With Automated Remediation
- Effective Team Work With Drag-and-Drop Control Assignment
- Get Real-Time Critical Alerts That are Specifically Relevant to You
- MSSPs Can Manage Multiple Clients Under One Platform
- Onboard a New Vendor in Just 30 Seconds
- Turn Hours of Work Into Seconds with Centraleyes Vendor Risk Profile
- Always Informed with Centraleyes Domain Benchmarking
- Microsoft Responsible for Made-in-China Hack that Targeted US Officials
- AI Gets an Endorsement from Coalition
- NIST NVD "Under Construction"
- TutaCrypt to Thwart 'Harvest Now, Decrypt Later' Attacks
- 9.8/10 Severity Flaw in Team City- Patch Now!
- Blackcat Claims Responsibility for the UnitedHealth Change Breach
- US Gov's Cyber Survival Guide for Water Utilities
- Safeguarding Elections Amidst the Deepfake Deluge
- Faking the Figures (and the Faces): Deepfake Financial Frauds
- Trello Got a Scrape
- Advisory Issued for Androxgh0st Malware
- X Marks the Spot: Mandiant and SEC's Security Sway on Twitter
- Quantum Quandary: Navigating the Path to Unbreakable Encryption
- Chameleon Android Banking Trojan Morphs with Advanced Tactics, Expands Targets
- Ubiquiti Resolves User Access Bug
- The U.S. Needs a Better AI Plan
- Navigating the Cyber Currents: Ensuring a Watertight Critical Infrastructure
- Dollar Tree Breach: Supplier Roots Sprout Risks
- Applying Digital Pressure to Stop the “Citrix Bleed”
- 30-Year-Old Medical Protocol Making Headlines
- 88 Million Americans Affected in 2023 By Healthcare Data Breaches
- Critical Atlassian Flaw Has a Simple Fix
- D.C. Voter Data Leak: What We Know So Far
- Centraleyes Leads the Way with Full PCI DSS 4.0 Compliance Support on its Innovative Platform
- Will the Real Admin Please Step Up?
- Straightening Out the curl Vulnerability
- Vague in the Hague: Who Is Behind the ICC Data Breach?
- Forever 21 Discloses Data Breach Impacting Over Half a Million
- FBI on a Wild Duck Hunt after Qakbot
- The Enemy Within: Tesla’s Data Breach Was an “Inside Job”
- NIST CSF is Getting a Makeover
- Russia Prime Suspect for UK Electoral Commission Cyber Attack
- Storm-0558 Isn’t Over Yet
- Google-Owned VirusTotal Data Leak: Result of Human Error
- Made-In-China Hack Infiltrates the US Government
- EU-U.S. Data Privacy Framework: Is Adequate Good Enough?
- Anonymous Sudan Or Anonymous Russia?
- Over 100,000 ChatGPT User Account Credentials For Sale on the Dark Web
- Ransomware Causes St. Margaret Health’s Permanent Closure
- MOVEit Transfer Vulnerability Going Wild
- How to Build a Successful GRC Program to Help Reduce Your Risk Posture
- How to Stay Secure and Compliant in a World of Regulatory turmoil
- Don’t Keep Your Head in the Clouds – How to Protect Yourself from Virtual Risk
- Flash Webinar: How to Know When it's Time to Build a Risk Management Program
- Enhancing Cyber Risk Management Through the Power of Automation - Boutique Webinar
- Flash Webinar: From Technical to Business Risk - How to Communicate With Your Board
- Flash Webinar: What You Can Learn From the SolarWinds Attack to Lower Your Chances of Being Breached
- Flash Webinar: Supply Chain, 3rd-Party Vendors and the Silent Assassin Among Them
- Flash Webinar: Cyber Risk Management - it Doesn't Have to Be So Painful
- Understanding the Different Types of Audit Evidence
- Data Loss Prevention: Best Practices for Secure Data Management
- What is Maryland’s Online Data Privacy Protection Act?
- Enhancing Security and Reducing Costs with Advanced Zero Trust Implementation
- Navigating Legal Challenges of Generative AI for the Board: A Strategic Guide
- Exploring the Cost of a Data Breach and Its Implications
- Best 5 Privacy Management Tools for 2024
- Introduction to ISO 42001 and Its Impact on AI Development
- The Best SIEM Tools To Consider in 2024
- The 11 Best GRC Tools for 2024
- 8 Best Compliance Automation Tools: How to Choose
- The Best 10 Vendor Risk Management Tools
- Best 8 Vulnerability Management Tools for 2024
- Protecting Patient Data Post-Change Healthcare Breach
- Ensuring Business Resilience: Integrating Incident Response and Disaster Recovery Plans
- Understanding the Key Updates in NIST Cybersecurity Framework 2.0
- What's in the NIST Privacy Framework 1.1?
- The 5 C’s of Audit Reporting
- Cloud Compliance Frameworks: Ensuring Data Security and Regulatory Adherence in the Digital Age
- Generative AI Governance: Balancing Innovation and Ethical Responsibility
- Overview of AI Regulations and Regulatory Proposals of 2023
- Risk and Regulation: A Strategic Guide to Compliance Risk Assessment
- Understanding the ISO 27001 Statement of Applicability in Cybersecurity
- 5 Benefits of Identity and Access Management
- Unveiling the Threat Landscape: Exploring the Security Risks of Cloud Computing
- Future of Compliance: 2024's Essential Cybersecurity Insights
- What Do You Do if You Have a Third-Party Data Breach
- 7 Steps to Measure ERM Performance
- The EU AI Act: What It Means for Your Compliance
- How Do You Quantify Risk? Best Techniques
- How to Prepare for Compliance With the SEC Cybersecurity Rules Update
- Protecting Endpoints in an Evolving Threat Landscape
- The Goals of Security Compliance
- Data Privacy in the United States: A Recap of 2023 Developments
- Introduction to the NIST AI Risk Management Framework (AI RMF)
- NIS2 Framework: Your Key To Achieving Cybersecurity Excellence
- Comprehensive Third-Party Risk Assessment Checklist for Robust Risk Management
- New Jersey Privacy Act: What to Expect
- Strategies to Overcome Vendor Risk Assessment Challenges
- How to Get PCI DSS Certification?
- Cyber Leaders of the World: Chris Lockery, CISO at Help at Home
- Cyber Leaders of the World: Michael Anderson, CISO at the Dallas Independent School District
- Cyber Leaders of the World: Timothy Spear, Co-Founder and CTO of Whonome
- Cyber Leaders of the World: Marc Johnson, CISO at Impact Advisors
- Cyber Leaders of the World: Craig Williams, CISO at Secure Data Technologies
- Cyber Leaders of the World: Bill Genovese, CIO Advisory Partner at Kyndryl
- Cyber Leaders of the World: Dr. Brian Callahan, Graduate Program Director & Lecturer at ITWS@RPI, and CISO at PECE
- Cyber Leaders of the World: Chris Grundemann, Research Category Lead for Security and Risk at GigaOm
- Cyber Leaders of the World: Barak Blima, CISO at CHEQ
- Cyber Leaders of the World: Tony Velleca, CEO at CyberProof and CISO at UST
- Cyber Leaders of the World: Rob Black, CEO and Founder of Fractional CISO
- Cyber Leaders of the World: Zachary Lewis, CISO at the University of Health Sciences and Pharmacy in St. Louis
- Cyber Leaders of the World: Dan Wilkins, CISO at the State of Arizona
- Cyber Leaders of the World: Sagar Narasimha, CISO at Amagi
- Cyber Leaders of the World: Seema Sharma, Global Head of Information Security & Data Privacy at Servify
- Cyber Leaders of the World: Shay Siksik, VP of Customer Experience at XM Cyber
- Cyber Leaders of the World: Raz Karmi, CISO at SimilarWeb
- AI Auditing
- Data Exfiltration
- Data Sovereignty
- Control Objectives for Information and Related Technologies (COBIT)
- Audit Management Software
- Vendor Framework
- AI Governance
- AI Transparency
- Internal Penetration Testing
- Cybersecurity Automation
- GDPR Compliance Risk Assessment
- Audit Fatigue
- Compliance Operations
- Risk Management Automation
- Corporate Sustainability Reporting Directive
- Man-in-the-Middle Attack
- Digital Rights Management
- Content Disarm and Reconstruction
- Calculated Risk
- Data Residency
- Asset Risk Management
- Identity Security
- Risk Modeling
- CISO Board Report
- Risk Communication
- SOC 2 Bridge Letter
- Audit Documentation
- Enterprise Risk Management (ERM)
- Compliance Gap Analysis
- Security Misconfiguration
- Security Program Management
- Digital Risk Protection
- Advanced Persistent Threat
- Continuous Auditing
- Risk Control
- SSAE 16
- ISMS Awareness Training
- Risk Management Policy
- Risk Avoidance
- Resilience Management
- What are the main steps in the threat modeling process?
- What exactly is considered PHI according to HIPAA?
- What does the PCI Compliance Auditor Look At?
- How to Detect and Prevent Data Leakage?
- What are the Challenges Associated with Cloud Security Management?
- How Many Techniques Are There in MITRE Att&ck?
- What Are the Benefits of Conducting a Risk Assessment?
- What are the categories of controls in ISO 27001?
- How Does ABAC Differ From Other Access Control Models?
- What Does a Compliance Management System Look Like?
- What Are the NIST CSF Implementation Tiers?
- What is the Purpose of Compliance Attestation?
- How do I become NIST 800-171 compliant?
- Why are the three rules of HIPAA necessary?
- What are the seven categories of risk?
- What are the Six Types of Vulnerability Scanning?
- Which are the most important compliance frameworks?
- How do you implement GRC automation?
- How Can I Measure the ROI of Implementing a Compliance Solution?
- How do you determine whether HIPAA violations need to be reported?
- What are the three major threats to cybersecurity today?
- How Do You Manage Compliance Risk?
- How Does a GRC platform handle data privacy and security?
- How Often Should Supplier Risk Assessments Be Conducted?
- How is a SOC 2 Report Structured?
- What Are the Major Risk Factors in Cyber Security?
- How Do You Read a Risk Matrix Table?
- What is the Risk Rating Matrix Used For?
- What are the Benefits of Risk Assessment Software?
- How does the CMMC differ from NIST?
- What are the penalties for not reporting a HIPAA violation?
- What are the different versions of HECVAT?
- What are the 4 objectives of Enterprise Risk Management?
- Who needs to be ITAR compliant?
- What are the best practices for vendor risk management for CISOs?
- What are the three stages of the zero-trust security model?
- What are the NIST control families?
- Can ChatGPT replace compliance officers?
- How can thread modeling help an organization identify and mitigate potential risks?
- What is the average cost of penetration testing?
- Last Resources
Media
Whitepapers
Financial Institutions
In the financial services industry, data security is more essential than ever. Institutions have migrated to online…
Life Science
In recent years, as digital health solutions became more prevalent and in-demand, Life Science institutions have become…
Higher Education
Over the years, academic institutions adopted many new and advanced digital and technological solutions to provide staff,…
Platform Feature Reviews
Enhance Your Cyber Maturity With ITSM Integration and Automated Remediation
Centraleyes makes your data actionable and enhances your cyber maturity by automatically creating remediation workflows whenever a…
Ensure Your Ongoing Compliance With Automatic Framework Reassessment Tasks
Periodically reassessing your frameworks can be crucial to ensure your ongoing compliance and risk posture. With Centraleyes…
Stay in the Know With a Full Activity Log of Your Assessment Collection
The Centraleyes platform offers a full audit trail of all of the activities contained within your assessments,…
Add a New Entity to Perform Your Assessment in 10 Seconds
Creating a new entity in the Centraleyes Multi-Entity 1st Party module provides you with another layer of…
Cyber Leaders Publication
Cyber Leaders of the World: Chris Lockery, CISO at Help at Home
Please tell us a bit about yourself, your background, and your journey of becoming a CISO at…
Cyber Leaders of the World: Michael Anderson, CISO at the Dallas Independent School District
Please tell us about yourself, your background, and your journey of becoming a CISO for the Dallas…
Cyber Leaders of the World: Timothy Spear, Co-Founder and CTO of Whonome
Please tell us a bit about yourself, your background, and your journey of becoming a co-founder and…
Cyber Leaders of the World: Marc Johnson, CISO at Impact Advisors
Please tell us a bit about yourself, your background, and your journey of becoming a CISO at…
News and Updates
Microsoft Responsible for Made-in-China Hack that Targeted US Officials
A US government-backed investigation has determined that a China-sourced hack last year that infiltrated Microsoft’s networks and,…
AI Gets an Endorsement from Coalition
Coalition, a leader in cyber insurance, has added a positive endorsement for artificial intelligence (AI) to its…
NIST NVD "Under Construction"
In recent weeks, NIST’s National Vulnerability Database (NVD) has been experiencing a slowdown. Since February 15, 2024,…
TutaCrypt to Thwart 'Harvest Now, Decrypt Later' Attacks
Tuta Mail introduced TutaCrypt, a protocol engineered to bring email encryption into the post-quantum era. Tuta Mail…
On-Demand Webinars
How to Build a Successful GRC Program to Help Reduce Your Risk Posture
Watch this special, collaborated webinar session where Sagar Shah, Senior Manager of GRC at Corvus Insurance, and Yair Solow,…
How to Stay Secure and Compliant in a World of Regulatory turmoil
Watch this special, collaborated webinar session where industry experts from Netsurit and Centraleyes meet at an intriguing…
Don’t Keep Your Head in the Clouds – How to Protect Yourself from Virtual Risk
In todays world where many organizations have adopted and migrated most of their activity to the cloud,…
Flash Webinar: How to Know When it's Time to Build a Risk Management Program
Companies in hyper growth mode as well as mid-market enterprises are often focused on product development and…
Blog
Understanding the Different Types of Audit Evidence
Audit evidence lies at the heart of cybersecurity audits and assessments, providing tangible proof of an organization’s…
Data Loss Prevention: Best Practices for Secure Data Management
The stakes for safeguarding sensitive information have never been higher. Cyber Data loss can lead to severe…
What is Maryland’s Online Data Privacy Protection Act?
Maryland Takes the Lead in Privacy Legislation with Comprehensive MODPA The Maryland legislature enacted two comprehensive privacy…
Enhancing Security and Reducing Costs with Advanced Zero Trust Implementation
Traditional methods no longer suffice to protect sensitive data from modern threats. Conventional strategies relied on fortress-like…
Cyber Leaders
Cyber Leaders of the World: Chris Lockery, CISO at Help at Home
Please tell us a bit about yourself, your background, and your journey of becoming a CISO at…
Cyber Leaders of the World: Michael Anderson, CISO at the Dallas Independent School District
Please tell us about yourself, your background, and your journey of becoming a CISO for the Dallas…
Cyber Leaders of the World: Timothy Spear, Co-Founder and CTO of Whonome
Please tell us a bit about yourself, your background, and your journey of becoming a co-founder and…
Cyber Leaders of the World: Marc Johnson, CISO at Impact Advisors
Please tell us a bit about yourself, your background, and your journey of becoming a CISO at…